A Guide to ITAD Risk Reduction in Atlanta for 2026
Getting rid of old technology seems simple enough—just make some space for the new stuff, right? But it's not that easy. In reality, it's a minefield of risks that can come back to bite your business, hard.
A single lost hard drive can trigger a seven-figure data breach lawsuit. One misstep in compliance can lead to staggering fines. When you're dealing with old IT gear, a solid, proactive strategy isn't just a good idea; it's an absolute necessity. At GreenAtlanta.com, we believe that strategy should do more than just manage risk—it should create positive impact.
The Real Risks of Retiring Your IT Assets
When your company's computers, servers, and hard drives hit their end-of-life, the real work begins. The process, known as IT asset disposition (or ITAD), is packed with potential pitfalls that go way beyond just tossing out old equipment. For businesses here in Atlanta, getting this wrong opens the door to serious data, regulatory, environmental, and financial trouble.
Think about it: one lost laptop or a single misplaced hard drive can hold a treasure trove of sensitive information. We're talking customer PII, employee records, or your company's secret sauce—its proprietary IP. A breach could be catastrophic.
These aren't just hypotheticals. A local healthcare provider could face crippling HIPAA fines, while a financial firm might see its reputation shattered over a FACTA violation.
To make sense of it all, we've broken down the core risks into a few key categories.
Core Risks in IT Asset Disposition (ITAD)
| Risk Category | Description | Potential Consequence |
|---|---|---|
| Data Security | Retired assets still contain sensitive data, even after a factory reset. This includes customer PII, financial records, employee information, and intellectual property. | Massive data breach fines (GDPR, CCPA), seven-figure lawsuits, loss of customer trust, and severe reputational damage. |
| Regulatory Compliance | Failure to adhere to industry-specific regulations like HIPAA, FACTA, or SOX, which mandate secure data destruction and proper disposal methods. | Steep financial penalties from regulatory bodies, potential criminal charges, and suspension of business operations. |
| Environmental | Improperly dumping e-waste leads to toxic materials like lead and mercury contaminating soil and water, violating EPA and state regulations. | Heavy fines for environmental non-compliance, negative press, and damage to your brand's reputation as a good corporate citizen. |
| Operational | Lack of a clear chain-of-custody process means assets can get lost, stolen, or mishandled, creating gaps in your inventory and security logs. | Inability to prove compliance during an audit, internal security vulnerabilities, and wasted resources tracking down missing equipment. |
Each of these risks carries a heavy weight. A single failure in any one area can have a domino effect, impacting your finances, reputation, and legal standing all at once.
Data Security and Compliance Failures
The most obvious and immediate danger is the data left on your old gear. A lot of folks think a simple factory reset wipes the slate clean, but that’s a dangerous myth. It’s surprisingly easy to recover data from a "wiped" drive, leaving your organization wide open.
Just imagine an Atlanta law firm tossing old office PCs into a commercial dumpster behind their building. A rival, or any opportunistic scammer, could easily grab those hard drives, pull sensitive case files, and expose confidential client data. The legal fallout and the hit to their credibility would be almost impossible to recover from.
This kind of thing happens far more often than you'd believe. It's why having a certified data destruction process is no longer optional—it's a fundamental part of modern risk reduction. Your ITAD partner absolutely must give you verifiable proof that every single byte of data was destroyed for good.
Environmental and Reputational Damage
Data isn't the only thing you need to worry about. Environmental rules are a huge piece of the puzzle. Electronics are full of nasty stuff like lead and mercury, and if they end up in a landfill, they can poison local soil and water. The EPA doesn't take kindly to that, and the fines can be substantial. You can learn more about the environmental impact of electronic waste in our detailed guide.
The damage to your company's image can be just as bad. No one wants to be known as the business that pollutes the community.
This is all about proactive risk management. Think of it this way: between 2000 and 2019, the world saw 7,348 major disasters, costing an estimated $2.97 trillion. Smart organizations learned to prepare for catastrophes instead of just reacting to them. The same logic applies here. You have to actively divert e-waste from landfills to prevent a data or environmental disaster that's entirely avoidable.
Working with a certified ITAD provider like GreenAtlanta.com turns this whole mess from a liability into a secure, compliant process. We make sure every device is handled the right way, protecting your business and boosting your ESG goals.
Even better, our dual-impact model supports veteran aid and reforestation projects. It transforms a risk management task into a powerful story of corporate citizenship—"Recycling That Restores Lives and Landscapes."
Building Your Ironclad ITAD Policy
A formal, written IT Asset Disposition (ITAD) policy is your single most powerful defense against compliance nightmares, data breaches, and costly human error. Think of it as the official playbook that ensures everyone in your organization—from IT to legal—handles retiring tech the exact same way, every single time. This isn't about grabbing a generic template; it’s about crafting a practical guide built for your Atlanta-based operations to achieve maximum risk reduction.
An effective policy does more than just say, "get rid of old computers." It gets specific, assigning clear roles and creating a paper trail you can actually verify from an asset's first day to its last. Without a documented policy, you're just relying on institutional knowledge and guesswork. That's a huge gamble no business can afford to take.
Defining Asset Tiers and Data Sensitivity
First things first: you have to acknowledge that not all tech assets are created equal. A customer-facing kiosk in your lobby is a world away from a back-office server packed with sensitive client financial data. A smart ITAD policy reflects this by sorting assets into tiers based on risk.
Tier 1 High-Risk Assets: These are your crown jewels. We’re talking about devices holding Personally Identifiable Information (PII), Protected Health Information (PHI), financial records, or invaluable intellectual property. Think servers, executive laptops, and hard drives from the finance or HR departments. These assets demand the absolute highest level of security, including mandatory, certified data destruction.
Tier 2 Medium-Risk Assets: This bucket includes devices with company data that's proprietary but not necessarily regulated or personally sensitive. This might be a marketing team's workstations with project files or internal development machines. They still need secure data wiping to a set standard, but they could be good candidates for refurbishment and resale.
Tier 3 Low-Risk Assets: These are your non-data-bearing devices. Things like monitors, keyboards, mice, and printers fall into this category. For these, the primary concern isn't data sanitization; it's ensuring they are recycled in an environmentally responsible and compliant way.
By tiering your assets, you give your team a clear, immediate roadmap. When an employee needs to retire a laptop, they can instantly see its risk level and know exactly which protocol to follow. It removes the ambiguity, which is a cornerstone of any solid risk reduction strategy.
Mandating Standards and Assigning Roles
Your policy has to get into the weeds on how data is actually destroyed. Vague instructions like "wipe the drives" are a recipe for disaster. You need to mandate a specific, recognized standard for data sanitization. The gold standard in the industry is NIST 800-88, a set of guidelines from the National Institute of Standards and Technology that ensures data is truly gone and forensically unrecoverable.
Just as critical is assigning clear ownership. Who does what?
A strong ITAD policy acts as an internal service level agreement (SLA). It clearly outlines who (e.g., the IT department) is responsible for tagging and inventorying assets, who (e.g., the compliance officer) is responsible for verifying Certificates of Destruction, and who has the final sign-off.
This clarity is what prevents devices from slipping through the cracks. It guarantees that every step, from a PC being unplugged at a desk to receiving its final destruction certificate, is owned by a specific person or team. For more insights on this topic, check out our guide on IT asset management best practices.
Case Study: An Atlanta Healthcare System's Audit Success
Let me give you a real-world example. A large Atlanta-based healthcare system recently went through a massive equipment refresh, retiring over 1,500 devices. Because they had a meticulously detailed ITAD policy, they sailed through a surprise HIPAA audit that followed.
Their policy was crystal clear: on-site hard drive shredding for any device containing PHI (Tier 1), NIST-compliant wiping for all administrative PCs (Tier 2), and a full, serialized audit trail for every single asset.
When the auditors showed up, the compliance team was ready. They produced a complete chain-of-custody log and individual Certificates of Destruction for every device in question. This documentation didn't just show they were compliant; it proved their mastery of risk reduction and turned a high-stress audit into a simple validation of their excellent processes. To streamline the creation of these essential agreements and strengthen your ITAD framework, consider utilizing a free AI contract generator to help formalize vendor relationships and responsibilities.
Finally, none of this works without executive buy-in. You have to frame the policy not as an IT cost center, but as an essential business insurance policy. It’s what protects the entire organization from financial penalties and reputational ruin. A well-defined policy, when it's actually enforced, becomes the bedrock of a secure and compliant IT lifecycle.
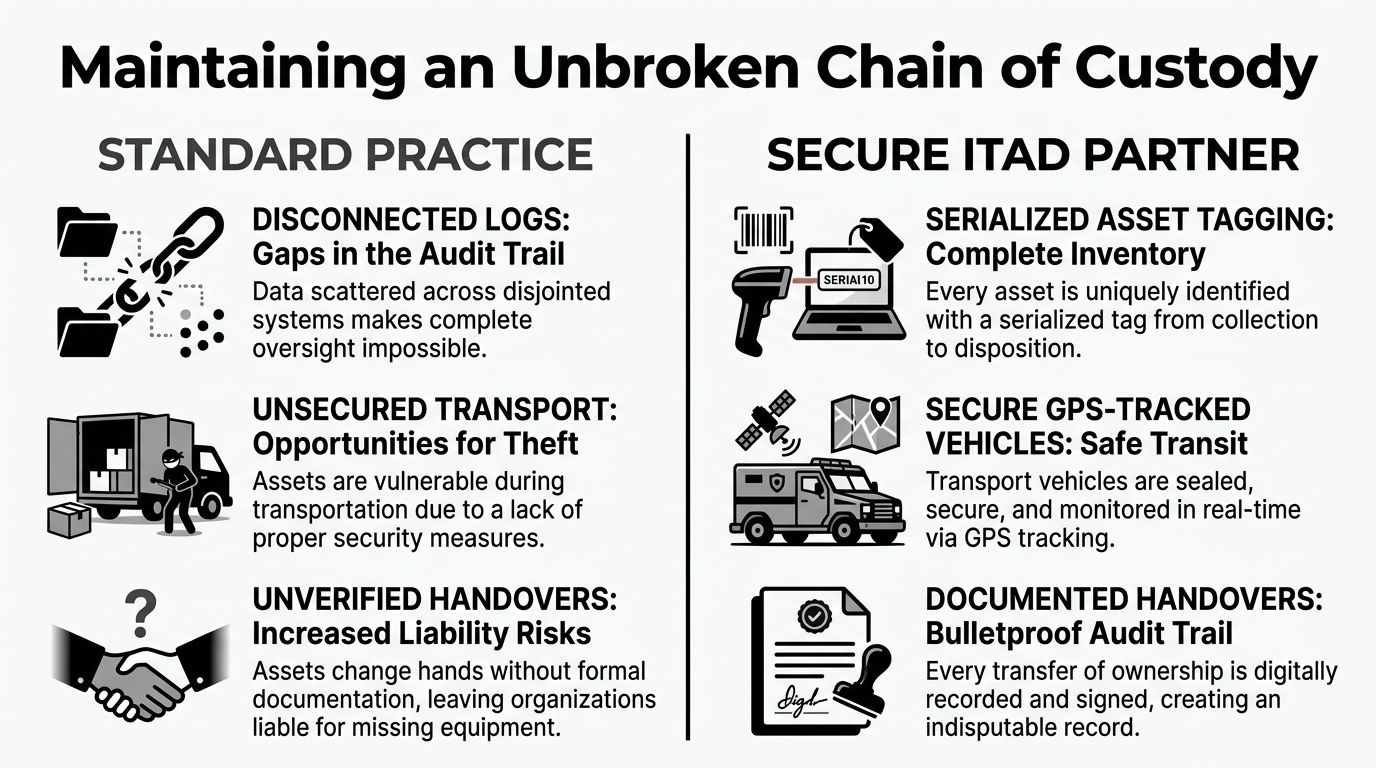
Maintaining an Unbroken Chain of Custody
The moment an IT asset leaves your direct control, it becomes a liability. That journey from an office desk to its final, certified destruction is full of security gaps. True risk reduction isn't just about what happens at the end; it's about sealing every single one of those gaps along the way with an unbroken, fully documented chain of custody.
We like to compare it to handling legal evidence. Every person who touches a piece of evidence must sign for it, track it, and secure it. If that chain breaks even once, the evidence is thrown out. For your business, a break in the chain of custody means your data—and your reputation—is on the line. One unverified stop or a single lost laptop can completely undermine all your internal security work.
The Critical First Steps On-Site
Your chain of custody doesn't start when a truck pulls away from the curb. It starts the second an asset is taken offline, right there in your own facility. This is the foundation of the whole process, and it needs to be handled with absolute precision.
A professional ITAD partner will begin by conducting a detailed inventory on-site. Here's what that should look like:
- Serialized Asset Tagging: Every single device gets its own unique serial number recorded. From massive servers down to individual hard drives, this creates a master list that becomes the single source of truth for the entire project.
- Secure Collection: Assets are immediately placed into locked, tamper-evident containers before they're even wheeled down the hall. This prevents anyone from accessing them while they're still on your property.
- Documented Handover: The exact moment your team hands the assets to the vendor is a critical transfer of liability. This needs to be formally documented with signatures from both sides, a timestamp, and a direct reference to the serialized inventory list.
This initial paperwork is your first line of defense. It's the proof of exactly what left your building and who took responsibility for it. Without this record, you're just operating on trust, which offers zero protection if an auditor comes knocking or a legal issue arises.
Demanding Secure Transit and Logistics
Once your assets are on the move, a whole new set of risks appears. Unsecured trucks and unvetted drivers are a data breach waiting to happen. This is exactly why you have to be demanding about the logistics protocols your ITAD vendor uses.
A truly secure logistics operation has a few non-negotiables. Your partner must use a dedicated fleet of GPS-tracked vehicles, giving you real-time visibility from your facility to theirs. The people handling your equipment shouldn't be random third-party contractors; they need to be uniformed, background-checked employees of the ITAD company itself. Anything else introduces another layer of unnecessary risk.
Then there's the destination. The receiving facility must have iron-clad access controls, including secure, monitored loading docks and internal checkpoints to stop any unauthorized entry. Every one of these steps fortifies the chain of custody, which is fundamental to overall risk reduction. You can see more details on what makes for a secure loading dock and receiving process in our deep-dive guide.
The entire process, from start to finish, has to be seamless and verifiable. It’s the only way to build the bulletproof audit trail you need to satisfy regulators, stakeholders, and your own peace of mind. Anything less is a gamble.
Choosing the Right Data Destruction Method
When it comes to getting rid of old IT assets, not all data destruction methods are created equal. Far from it. Choosing the right approach is one of the most important decisions you'll make in your entire risk reduction plan. This isn't a one-size-fits-all game; the best method really depends on the type of media, how sensitive the data is, and your specific compliance headaches.
Making the right choice means you can be certain that sensitive information is gone for good, not just tucked away. It's the difference between genuine, verifiable security and leaving a back door open for a potential data breach. Let's break down the main options you'll be weighing.
Software-Based Data Wiping
You might hear this called data sanitization. At its core, it's using specialized software to methodically overwrite every single sector of a storage device with junk data—usually random 1s and 0s. This can be done over and over again in multiple passes, making the original information forensically unrecoverable.
The most well-known standard is DoD 5220.22-M, a protocol once used by the U.S. Department of Defense. It’s a solid choice for traditional magnetic hard disk drives (HDDs), especially for assets you plan to resell or put back into service. Because the drive still works, you can capture some residual value while ensuring the data is gone.
The catch? This method takes time, sometimes hours per drive. It's also less reliable on modern Solid-State Drives (SSDs). Their internal wear-leveling technology can shuffle data around in ways that software wipes can miss, potentially leaving fragments of data behind.
Degaussing for Magnetic Media
For magnetic media like HDDs and old-school backup tapes, degaussing is a fast and brutally effective option. A degausser is a machine that unleashes a powerful magnetic field, instantly scrambling the magnetic orientation of the drive's platters. All data is neutralized in seconds. If you're curious about the nitty-gritty, you can learn more about what a degausser is and how it works in our deep-dive guide.
Degaussing has two major things going for it:
- Speed: It sanitizes drives in a flash.
- Effectiveness: For magnetic media, it's a high-security knockout punch.
The main trade-off is that the intense magnetic pulse also fries the drive's firmware, rendering the hardware completely useless. It's a fantastic choice for high-security scenarios where the device has zero resale value. Just remember, it does absolutely nothing for SSDs, which don't store data magnetically.
Physical Shredding for Ultimate Security
When there is absolutely no room for error and you need 100% verifiable destruction, nothing beats physical shredding. This industrial-grade process feeds hard drives, SSDs, and other media into a massive shredder that grinds them down into tiny, confetti-like metal fragments. There's no coming back from that—the data and the device it lived on simply cease to exist.
For any device that held Tier 1 data—think PHI under HIPAA, critical intellectual property, or state secrets—physical shredding provides the most definitive form of risk reduction. It gives you irrefutable, visual proof that the data is destroyed forever.
This is the gold standard for SSDs and any other high-risk device where a Certificate of Destruction needs to be backed by undeniable physical evidence. A good partner like GreenAtlanta.com can even bring a mobile shredder to your facility, so you can watch the destruction happen with your own eyes.
This chart really drives home the difference between a standard, often leaky, ITAD process and the airtight chain of custody a dedicated partner maintains.
As you can see, a secure partner closes all the gaps, turning a potential liability into a documented, verifiable process from the moment an asset leaves your control to its final disposition.
Having a knowledgeable ITAD partner is essential for navigating these choices. Here at GreenAtlanta.com, we help our clients select the perfect destruction method for each asset, ensuring total compliance and turning a complex security chore into a streamlined, worry-free process. This approach not only helps you meet your regulatory requirements but also supports our dual missions of aiding veterans and planting trees, transforming your e-waste into a force for good.
How to Vet Your Atlanta ITAD Partner
Choosing an IT Asset Disposition (ITAD) partner is one of the most critical decisions you'll make in your risk reduction plan. The right one acts as a trusted extension of your own security team. The wrong one, however, can quietly introduce catastrophic dangers.
For Atlanta-based businesses, this isn't just about getting the best price for old equipment. It's about finding a genuine ally who can shield you from the fallout of a data breach or a compliance penalty. You're not just offloading hardware; you're handing over the keys to your company's data. Their competence is your security.
Verify Certifications and Insurance
First things first, check their credentials. Any legitimate ITAD vendor operating in the Atlanta area will hold key industry certifications. These aren't just fancy logos for their website; they represent a public commitment to strict, audited processes for both security and environmental stewardship.
You absolutely want to see these two certifications:
- R2v3 (Responsible Recycling): This standard is a comprehensive framework covering environmental protection, data security, and the health and safety of workers. An R2v3-certified partner gives you peace of mind that your old tech won't end up in a landfill.
- e-Stewards: Often seen as the gold standard, e-Stewards has a zero-tolerance policy against exporting hazardous e-waste to developing nations. It's one of the toughest certifications to achieve.
Beyond certifications, it's time to talk insurance. Don't hesitate to ask for their Certificate of Insurance. You need to look for two specific policies: data breach insurance and pollution liability. A vendor operating without this coverage is essentially asking you to carry all the financial risk if something goes wrong.
Question Their Downstream Vendor Process
Here’s a fact: no single ITAD provider handles every last component themselves. They all work with a network of downstream partners to process specific materials, and this is where a lot of the hidden risk lies. You have to ask them point-blank, "How do you audit and manage your downstream vendors?"
A partner you can trust will have a transparent, fully documented process for vetting every single company in their supply chain. They should be able to show you audit reports and prove that their partners are held to the same high security and environmental standards they are.
If a potential vendor gets cagey about their downstream process or can't produce the paperwork, consider it a huge red flag. This transparency is what ensures your chain of custody remains unbroken and your risk reduction is complete.
History has shown us that ignoring low-probability, high-impact risks can be devastating. Think of the 2008 financial crisis, where banks that weren't prepared for a "black swan" event were simply ruined. The same logic applies to e-waste in Atlanta. Partnering with a certified recycler for secure data destruction and responsible disposal is how you can view risk in a broader historical context and turn a potential disaster into a manageable, documented process.
Schedule a Site Visit and Assess Their Value-Adds
Finally, nothing beats seeing an operation with your own two eyes. A site visit is non-negotiable. It’s your chance to inspect their physical security, watch how they handle intake and sorting, and meet the actual team you'll be working with. For more tips on what to look for, check out our breakdown of local IT asset disposition companies.
This is also your opportunity to see what else they bring to the table beyond just disposal. At GreenAtlanta.com, for example, we frame our service as a clear ESG win for our partners. We provide deliverables like our "Recycled with Purpose" digital badge and detailed impact reports that show how many trees were planted or veterans were supported through our partnership with USDA-approved reforestation projects and veteran aid nonprofits.
This approach turns a simple compliance task into a powerful story for your brand, all under our guiding principle: "Where Tech Meets Trees & Transformation."
Mastering Documentation for Audit Readiness
In the world of data security and regulatory compliance, there's an old saying that every seasoned pro knows by heart: if it isn't documented, it never happened. This final, but absolutely critical, part of your ITAD process is all about the paper trail. It’s what proves you did everything right.
Proper documentation is your best tool for risk reduction. It transforms all your careful security efforts from just actions into a solid, verifiable defense that will stand up to any audit.
Without that paper trail, you're leaving your organization wide open. An auditor’s simple request for records can send your team into a panic, and a lack of evidence can quickly escalate a routine check into a full-blown compliance failure, complete with hefty fines. Your ITAD partner is your first line of defense here; they are responsible for providing the definitive proof that every asset was handled securely from the moment it left your sight.
Essential Documents for Your Audit File
A truly competent ITAD partner will provide a comprehensive documentation package after every single job. This isn't just a simple receipt—it’s your legal and compliance shield, and it needs to be organized for immediate access if an auditor comes knocking.
Here are the core documents you should always demand and keep on file:
Serialized Certificates of Destruction (CoD): This is the big one. It can’t be a generic, one-size-fits-all statement. It must be a detailed report that lists every single asset by its unique serial number and confirms the exact date and method of destruction (e.g., physical shredding or a NIST 800-88 compliant wipe).
Asset Transfer Forms: These forms are the backbone of your chain of custody. They document the precise moment your assets left your facility and were officially accepted by your vendor. Non-negotiable elements include clear signatures and timestamps from both parties.
Environmental Compliance Reports: This report proves your commitment to environmental stewardship. It should confirm that all non-data-bearing parts and any hazardous materials were recycled in accordance with EPA and local regulations.
Think of this documentation as an insurance policy. You hope you never have to use it during a tense audit, but if that day comes, its value is immeasurable. A complete, well-organized file proves your due diligence and can stop a tough regulatory inquiry dead in its tracks.
Beyond Compliance: The ESG and CSR Advantage
While ticking compliance boxes is the main reason for all this paperwork, a forward-thinking partner sees an opportunity to do more. This is where your risk reduction strategy can actually become a powerful story for your brand. At GreenAtlanta.com, we believe in turning a routine disposal process into a compelling narrative of positive social impact.
We don't just stop at the standard compliance documents. We provide our partners with unique, shareable reports that quantify the good they're doing. This transforms your company’s e-waste disposal from a cost center into an easy ESG win.
For example, our corporate partners also receive:
Veteran Support Impact Reports: These documents show exactly how your e-waste contributions have helped fund our veteran aid programs, giving your Corporate Social Responsibility (CSR) team tangible data to share.
Plant-A-Tree Certificates: We issue personalized certificates that detail the number of trees planted in your company’s name, directly connecting your recycling efforts to real-world reforestation wins.
This approach transforms your ITAD documentation. It’s no longer just a boring record of compliance, but a valuable asset for your marketing and ESG teams. It’s proof that you’re not just managing risk—you’re "Turning E-Waste into Hope."
Common Questions We Hear on the Ground
Over the years, we've helped countless Atlanta businesses get a handle on their ITAD process. A few questions pop up time and time again as companies work to lock down their risk reduction strategy.
What’s the Single Biggest E-Waste Mistake Atlanta Companies Are Making?
Hands down, it's underestimating the risk hiding in plain sight on old hard drives. It’s a classic story: a business assumes a quick factory reset is “good enough,” or worse, they shove old equipment into a storage closet to be dealt with “later.”
That closet full of old tech isn't just a mess—it's a ticking time bomb for a data breach. Every single retired device that holds data, from a server rack to a company phone, must be treated as a serious liability until it's been professionally sanitized or destroyed. And you need the paperwork to prove it.
How Can I Be 100% Sure Our Company's Data Is Really Gone?
True peace of mind comes from working with a certified ITAD partner who is completely transparent about their destruction methods. For any high-risk devices loaded with your most sensitive information, don't settle for anything less than physical shredding. You should even have the option to witness the process yourself.
What about assets you hope to reuse or resell? For those, you'll want to insist on a data wiping process that meets or, ideally, exceeds the NIST 800-88 standard. The non-negotiable final step is getting a serialized Certificate of Destruction. This document should list every single asset by its unique serial number, giving you an auditable record of its final fate.
Does a Small Business Really Need a Formal ITAD Policy?
Absolutely. Data breach penalties and environmental regulations don't scale down for smaller companies. Having even a simple, one-page policy is infinitely better than having no plan at all. It establishes clear, enforceable rules and demonstrates due diligence if regulators ever come knocking.
For a small Atlanta business, a policy can be as straightforward as this: "All company devices containing data will be disposed of via our certified e-waste partner, and a Certificate of Destruction must be kept on file for every asset."
That one sentence can dramatically lower your risk profile and start building a real culture of security inside your organization.
Ready to turn your ITAD risks into a secure, compliant, and impactful process? Partner with GreenAtlanta.com for a solution that protects your business while restoring lives and landscapes. Our messaging is simple: “Your old tech can house a veteran and grow a forest.” Schedule your pickup today at https://www.greenatlanta.com.