Atlanta Secure Data Destruction Services Guide
For an Atlanta CIO, secure data destruction stops being a back-office cleanup task the moment you attach real breach economics to a retired laptop, failed server, or forgotten backup drive. The average cost of a U.S. data breach exceeds USD 4.45 million, and it rises above USD 6 million for regulated sectors such as healthcare and finance, according to secure data destruction analysis for U.S. businesses. That’s the right lens for this Atlanta Secure Data Destruction Services Guide. Old devices don’t just hold scrap value. They hold liability.
Atlanta companies also have an opportunity that many procurement teams miss. If you choose the right destruction and recycling partner, end-of-life IT can support audit readiness, reduce landfill exposure, and contribute to a stronger ESG and brand story. For companies that want more than disposal, the best programs connect secure handling with visible outcomes such as reforestation support, veteran-focused giving, and CSR documentation your communications team can effectively use.
Why Secure Data Destruction is Non-Negotiable in Atlanta
Atlanta organizations retire far more data-bearing equipment than many leadership teams realize. In one refresh cycle, a company can move laptops, failed SSDs, copier drives, firewall appliances, backup media, and test hardware out of production. If even a small portion of that inventory leaves the business without verified sanitization or destruction, the exposure is not theoretical. It becomes a governance failure with security, legal, and reputational consequences.
This matters more in Atlanta because the local economy runs on regulated and operationally sensitive data. Healthcare providers, financial firms, universities, logistics operators, legal practices, and public-sector contractors all handle information that can trigger notification duties, contractual disputes, or audit problems if retired devices are mishandled. A city with distributed offices, hybrid work, and frequent growth creates more handoff points, and every handoff point needs control.
Risk Originates from Ordinary Devices
Serious incidents often start with equipment nobody considered high priority. The laptop in a storage room. The failed server drive waiting on an RMA decision. The copier hard drive that facilities sent out with other surplus items. The external disk used for a one-time migration.
The pattern is usually operational, not dramatic:
- Untracked storage during moves: Devices get boxed, shelved, or relocated without being reconciled to the asset register.
- Wrong downstream vendor: A recycler may handle commodities well but lack chain-of-custody procedures, serialized reporting, or media-specific destruction controls.
- Split ownership: IT, facilities, procurement, and office managers each handle part of the retirement process, but no single team owns the final proof.
- Missed edge assets: Lab systems, network appliances, badge systems, and multifunction printers often fall outside the standard endpoint workflow.
Practical rule: If a device ever stored credentials, customer records, employee data, financial information, or internal files, treat retirement as a security-controlled process.
The environmental side matters too. Devices that leave the business without proper downstream handling can undercut both compliance and ESG claims. Companies that want their disposal program to stand up to board scrutiny should understand the broader environmental impact of electronic waste.
Failures usually happen before the drive is destroyed
Executives often focus on the destruction event itself. In practice, the bigger weakness is what happens earlier: weak inventory controls, inconsistent custody, and missing documentation. If the chain is broken before the asset reaches the destruction floor, even a properly shredded drive does not fix the audit gap.
A sound program protects four business interests at the same time:
| Business need | What failure looks like | What good practice looks like |
|---|---|---|
| Security | Retired assets leave with recoverable data or uncertain handling history | Media is identified correctly, then sanitized or physically destroyed under documented controls |
| Compliance | No asset-level evidence of what happened, when it happened, or who handled it | Certificates, serial-number reporting, and custody records support audits and legal review |
| Operations | Refresh projects stall because pickup, packaging, and approvals are unclear | Decommission steps are scheduled, assigned, and tied to project timelines |
| Reputation | Public ESG messaging conflicts with opaque disposal practices | Secure recycling and documented downstream accountability support a credible sustainability story |
The strategic upside becomes apparent. The right partner does more than remove liability. A well-structured ITAD and destruction program can also produce materials your ESG, communications, and procurement teams can use: recycling documentation, diversion reporting, and visible community outcomes. For Atlanta companies, that can include partnership models tied to veteran support and reforestation, which turn end-of-life IT from a quiet cost center into a credible brand asset.
The mistake I see most often is simple. Teams classify retired equipment as surplus property before they classify it as sensitive media. Atlanta CIOs get better results when they reverse that order.
Understanding Data Destruction Methods from Wiping to Shredding
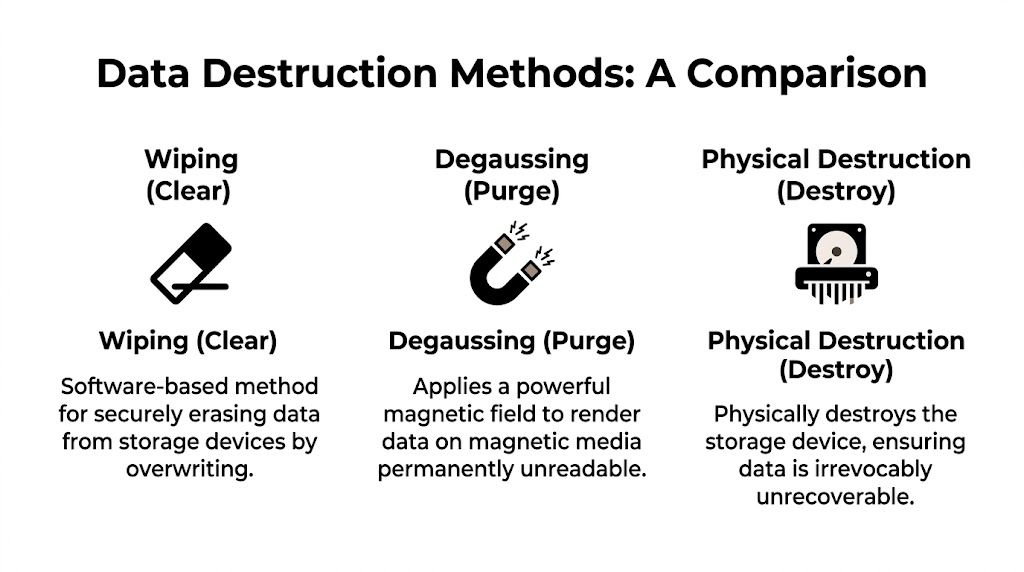
A single word, "destroyed," often hides the decision that matters most. Can this media be reused, or does the risk profile require irreversible destruction? Under NIST SP 800-88 Rev. 1, data sanitization falls into three categories: Clear, Purge, and Destroy, as summarized in this Atlanta certificate of destruction and NIST reference. Atlanta CIOs should treat those categories as operating choices tied to media type, data sensitivity, remarketing value, and audit exposure.
Clear works when reuse still has value
Clear usually means software-based overwriting. This method fits assets headed for internal redeployment, employee purchase programs, or resale, where preserving device value matters and policy permits logical sanitization.
That trade-off is important. A properly wiped laptop can return value to the organization and keep equipment in service longer, which supports sustainability targets. It also gives procurement and ESG teams something tangible to report: reuse instead of early destruction.
Clear is not the default answer for every asset. It depends on the device being functional, the sanitization process being verifiable, and the underlying storage type being suitable for the method used. Older shorthand such as "DoD wipe" still shows up in conversations, but the better question is whether the chosen process matches your current policy and the media in front of you.
Purge is for cases where recovery risk has to drop further
Purge is the middle ground between resale-friendly sanitization and physical destruction. In practice, this often includes degaussing for magnetic media or other methods intended to make data recovery impractical even with advanced techniques. The same NIST-based reference notes that degaussing is used where organizations want a lower chance of recoverability than standard overwriting provides.
This is the point where many internal teams make a category error. They ask for "wiping" on media that either cannot be wiped reliably or should not be reused in the first place.
If your team needs a plain-language explainer on the hardware involved, this overview of what a degausser does in data destruction workflows is a useful starting point.
A practical caution matters here. Degaussing applies to magnetic media. It does not solve for SSDs, flash storage, or every mixed-load environment. A competent Atlanta ITAD provider should be able to separate HDDs, SSDs, failed drives, tapes, and embedded storage, then explain why each stream gets wiped, purged, or destroyed.
Destroy removes the asset value and the uncertainty
Destroy means the media itself is physically rendered unreadable. The same source notes that shredding to ≤2mm is cited as a NAID AAA benchmark for media destruction, with the goal of making recovery infeasible.
Executives tend to understand this method immediately because the result is final. There is no resale value, but there is also far less ambiguity for failed drives, regulated data sets, damaged devices, and media with unclear handling history.
That finality has business implications beyond security. Physical destruction closes the door on remarketing revenue, but it can also reduce internal debate, shorten legal review, and give communications teams a cleaner ESG narrative when destruction is paired with documented recycling and downstream accountability. For Atlanta companies working with mission-aligned vendors, even this end state can support a stronger story around responsible recycling, veteran support, and reforestation.
Here is the practical comparison:
| Method | Best use case | Main advantage | Main limitation |
|---|---|---|---|
| Clear | Reuse, redeployment, resale | Preserves asset value | Lower margin for error on unsuitable media or higher-risk data |
| Purge | Higher sensitivity on compatible media | Stronger sanitization outcome | Limited to specific media types and equipment |
| Destroy | End-of-life, failed media, maximum assurance | Clear finality and low recovery risk | Eliminates reuse and resale value |
Match the method to the media, not the habit
The right choice starts with media identification, not vendor preference or internal routine. Failed SSDs, broken drives, encrypted but damaged laptops, backup tapes, and mixed pallets from office closures rarely belong in a one-size-fits-all workflow.
I advise clients to make the decision in this order: identify the media, classify the data, determine whether reuse is allowed, and then choose the sanitization method. That sequence protects the organization and usually produces better financial results. Reusable assets can be wiped and remarketed. High-risk or nonfunctional media can be destroyed with less debate. The result is a cleaner audit trail and a stronger ESG story because the company can show where it preserved value and where it chose certainty.
How to Choose a Certified Data Destruction Partner in Atlanta
Vendor selection gets easier when you stop asking, “Who can pick this up?” and start asking, “Who can defend this process in an audit, an investigation, or a board meeting?” That shift changes everything. It moves the conversation from trucking and recycling to controls, evidence, and accountability.
Ask for certifications, then ask how they operate
A vendor may list certifications on a website, but the more useful question is how those certifications show up in daily handling. Ask them to walk you through intake, scanning, packaging, transport, processing, and reporting.
Use questions like these in the first call:
- What standards govern your sanitization methods? You want explicit alignment to NIST, not vague language about “military-grade” practices.
- Which services are available by media type? Good partners separate HDDs, SSDs, failed drives, backup media, and mixed loads instead of forcing one generic process.
- How do you maintain chain of custody? Listen for serialized tracking, controlled handling, documented transfers, and restricted processing areas.
- What proof do we receive at the end? A serious provider issues a detailed Certificate of Destruction and related audit documentation.
If your team is comparing local providers, this directory-style overview of IT asset disposition companies in Atlanta can help frame the market, but the shortlist should come from documented controls rather than proximity alone.
Demand evidence, not reassurance
The best vendors are comfortable with scrutiny. They don’t dodge process questions. They expect them.
Ask to see examples of:
- Certificate format: The document should identify assets, dates, methods used, and compliance assertions in plain language.
- Exception handling: What happens when asset tags are missing, serial numbers are unreadable, or devices arrive physically damaged?
- Witness options: Can your team observe destruction onsite or through recorded verification if your policy requires it?
- Downstream handling: After data-bearing material is destroyed, how are residual commodities processed?
One practical benchmark from the verified data is worth keeping in mind. Providers operating with strong ITAD discipline use serialized tagging, GPS-tracked transport, and issue Certificates of Destruction that record serials, methods, and dates. That’s the level of specificity procurement should expect, not treat as a premium extra.
If a vendor answers a chain-of-custody question with marketing language instead of process language, keep shopping.
Choose a partner that can support ESG reporting too
The conversation takes a more strategic turn. Many companies still separate security disposal from sustainability and CSR reporting. That split creates more work and leaves value on the table.
A stronger vendor conversation includes questions such as:
- Can you document landfill diversion and downstream recycling practices?
- Can you support internal ESG or CSR reporting with usable summaries?
- Do you offer cause-based recycling programs that align with our brand values?
- Can our company participate in campaigns tied to veteran support or reforestation outcomes?
That last point matters more than it may seem. If your company already publishes ESG updates, hosts employee volunteer programs, or runs annual community campaigns, e-waste disposition can become part of that public narrative. Programs built around themes like “Recycle for a Cause,” tree-planting certificates, or veteran-support impact reports turn a compliance purchase into something your HR, marketing, and investor relations teams can use.
One provider in the Atlanta market, Atlanta Green Recycling, offers secure data destruction, IT equipment removal, de-installation, and electronics recycling workflows that can fit enterprise disposition projects. That kind of vendor profile becomes more useful when procurement asks for both destruction controls and post-project reporting, instead of treating those as unrelated needs.
Managing the Logistics of Secure IT Asset Disposition
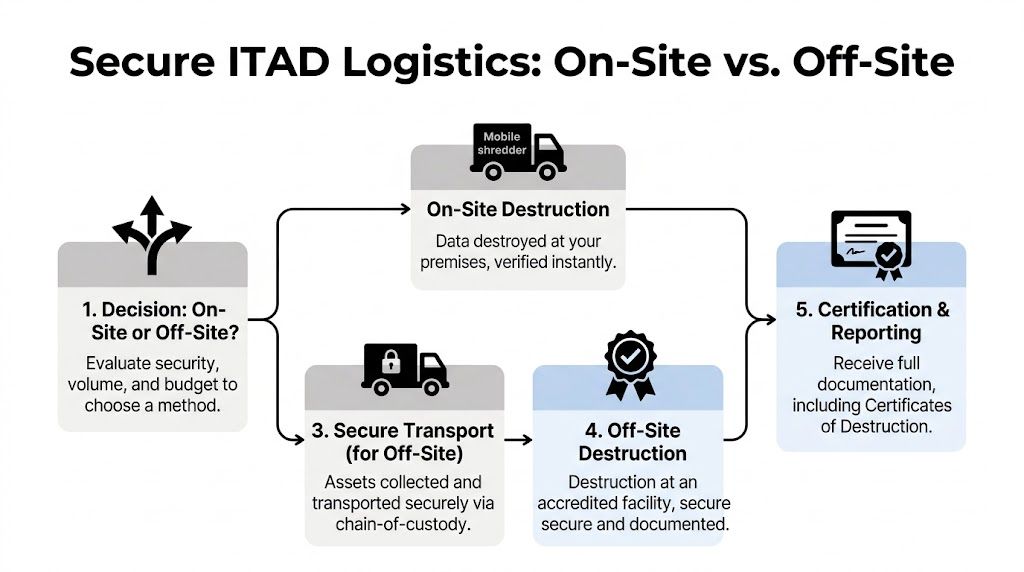
Most data destruction failures happen in transit, staging, or handoff. The destruction method may be solid, but the path to that method is weak. A secure ITAD process has to read like one continuous chain, from the moment an asset is pulled from production until the final certificate is filed.
Onsite and offsite each solve different problems
Onsite destruction gives security teams immediate closure. The media never leaves your premises intact, and your staff can witness the event. This works well for highly sensitive lots, failed drives, and clients whose legal or compliance policies demand direct verification.
Offsite destruction can be the better choice when volume is high, dock access is straightforward, and a certified processing facility offers better throughput. In those cases, the risk question shifts from “Where is destruction happening?” to “How strong is custody before destruction happens?”
A clear operational decision often comes down to three variables:
| Logistics factor | Onsite | Offsite |
|---|---|---|
| Immediate verification | Strong | Depends on reporting and evidence |
| Facility throughput | More limited | Often better for large volumes |
| Space and access needs | Requires onsite coordination | Requires secure loading and transport |
If your building team is involved in pickups, site access matters more than many IT managers expect. Loading docks, freight elevators, after-hours access windows, and secure staging all influence how smoothly a project runs. For larger removals, practical dock coordination is often the difference between a clean event and a messy one. This guide to commercial loading dock logistics for equipment removal is worth sharing with facilities before project day.
Chain of custody needs to be visible
Strong chain of custody isn’t a slogan. It’s a sequence of documented controls that your team can verify.
Look for this pattern:
- Asset identification at pickup: Devices are counted, tagged, and tied to a manifest.
- Controlled packaging: Media is secured in locked containers or sealed transport units.
- Documented transfer: Custody changes are recorded by date, time, and responsible personnel.
- Secure transportation: Vehicles and handling procedures support traceability and restricted access.
- Final processing record: The destruction or sanitization result maps back to the original inventory.
For data center decommissioning, office consolidations, and campus refreshes, these details matter even more because multiple internal teams are involved. IT, security, procurement, legal, facilities, and property management often touch the same project. A vendor that can coordinate de-installation, packing, and disposition under one workflow reduces confusion and closes gaps.
The safest project is the one where every handoff is boring because every handoff is documented.
Beyond Compliance Turning E-Waste into an ESG Win
A narrow procurement view sees data destruction as a cost. A stronger executive view sees it as a chance to align security operations with public commitments on sustainability and community impact.
That doesn’t mean softening the security requirement. It means adding value once the security baseline is locked in.
The best ESG stories start with real operational work
Annual sustainability reports are full of big goals and vague language. Secure electronics disposition is different because it’s tangible. You can point to retired assets, chain-of-custody records, recycling outputs, and project documentation. That gives your ESG team something concrete to include instead of another abstract commitment.
For Atlanta companies, this becomes more compelling when the vendor relationship includes a social mission. A program built around veteran support and tree planting gives your business a cleaner way to communicate what happened after devices left your office. The message is straightforward: your company protected data, kept electronics out of the waste stream, and supported visible community outcomes.
What a stronger partnership can produce
A mission-driven recycling and destruction program can generate useful collateral for several internal teams:
- For CSR reporting: Plant-a-tree certificates, diversion summaries, or impact reports tied to a recycling event.
- For employer brand: Employee-facing campaigns around Earth Day, Arbor Day, or Veterans Day.
- For sales and marketing: A “Recycled with Purpose” digital badge or concise sustainability language for proposals and websites.
- For community relations: Joint drives with schools, nonprofits, veteran organizations, or municipal programs.
There’s a reason this works. Unlike many ESG initiatives, electronics recycling starts with a necessary operational activity. The budget already exists. The improvement comes from choosing a partner who can document both secure handling and broader impact.
A local starting point for that conversation is electronics recycling in Atlanta for business equipment and e-waste programs, especially if your company wants to combine secure disposition with a broader office sustainability effort.
“Recycle for a Cause” works when it’s backed by custody records, destruction proof, and a credible downstream story.
What doesn’t work
Green marketing without documentation fails quickly. If your company wants to mention veteran support, tree planting, or environmental benefit, make sure the underlying recycling workflow is defensible. PR should sit on top of compliance, not replace it.
The right sequence is simple. First, secure the data. Second, process the equipment responsibly. Third, package the impact story in a form that legal, compliance, and communications can all live with.
Your Atlanta Data Destruction Procurement Checklist
Procurement teams do better with a checklist than with a pile of vendor brochures. Use this list before you approve any Atlanta secure data destruction provider.
Security and compliance checks
- Verify standards alignment: Ask the vendor to specify which sanitization methods map to Clear, Purge, or Destroy in their workflow.
- Confirm media-specific handling: Make sure HDDs, SSDs, failed media, backup devices, and mixed loads don’t all get treated as the same category.
- Review certificate detail: Request a sample Certificate of Destruction and check whether it includes serial numbers, methods, and dates.
- Test exception handling: Ask what happens when a drive is unreadable, missing a label, or physically damaged.
Logistics and operations checks
- Map the pickup path: Confirm who packs, labels, moves, and signs off on assets inside your building.
- Check custody controls: Require documented transfer points, secure staging, and traceable transport.
- Match service model to project type: Use onsite services when immediate witnessed destruction matters. Use offsite processing when scale and facility throughput matter more.
- Include facilities early: Large pickups fail when IT plans the project without loading dock, elevator, and access coordination.
Reporting and documentation checks
Use this as a fast screen in vendor meetings:
| Document or proof | Why it matters |
|---|---|
| Sample Certificate of Destruction | Shows how audit-ready the final record will be |
| Asset manifest process | Confirms how devices are tracked from pickup to processing |
| Chain-of-custody documentation | Demonstrates whether handoffs are controlled and reviewable |
| Recycling downstream summary | Supports environmental reporting and vendor due diligence |
ESG and brand checks
- Ask for impact reporting: If your company publishes CSR or ESG updates, request documentation you can reuse internally.
- Look for cause-based programs: Veteran support or tree-planting initiatives can turn routine recycling into a stronger employee and community story.
- Plan seasonal campaigns: Tie refresh cycles to Earth Day, Arbor Day, or Veterans Day if communications value matters.
- Request reusable assets: Certificates, digital badges, and concise impact summaries help your team communicate outcomes without stretching claims.
A good vendor shouldn’t struggle with any of these questions. If they do, the issue usually isn’t presentation. It’s process.
Frequently Asked Questions about Atlanta Data Destruction
Some of the most important procurement questions arise late in the process. They usually surface after budget is set, the refresh plan is approved, and someone asks what proof the company will have if a regulator, customer, or board member reviews the project six months later.
What are the latest Georgia updates affecting healthcare and government clients
Healthcare systems and public agencies in Georgia should expect tighter scrutiny around audit trails, especially for retired devices that held regulated data. One Georgia-focused secure data destruction update notes increased attention on serial-level tracking, stronger verification records, and documentation that can stand up to internal review and external inquiry, according to this Georgia-focused secure data destruction update.
For CIOs, the practical issue is vendor evidence. A provider may be able to destroy drives correctly and still create a problem if its reporting package is thin, inconsistent, or disconnected from your asset inventory. That gap slows approvals and creates friction with compliance, legal, and procurement.
Does this change how early we need to schedule projects
Yes. Organizations handling protected health information, criminal justice data, tax records, or other sensitive public records should lock down reporting requirements before pickup is scheduled.
The failure point is often simple. The destruction happened, but the certificate format, asset manifest, or custody record does not match what internal stakeholders expected.
This comes up often in hospital refreshes, clinic moves, agency surplus events, data center decommissions, and mixed-media cleanouts. In Atlanta, where projects often involve multiple sites and shared building access, that documentation issue can delay the whole disposition cycle.
What’s the difference between a recycler and a certified ITAD partner
The difference is control.
A recycler is usually built around commodity processing and material recovery. A certified ITAD partner is built around accountable handling of data-bearing assets first, then resale, recycling, or destruction based on condition and policy. Both may accept the same equipment. They are not managing the same risk.
Ask how the vendor tracks serialized assets, who signs custody at each handoff, what standard it uses for sanitization, and what happens to devices with resale value. Those answers tell you more than a marketing brochure will.
Is it safe to smash old hard drives with a hammer
It is a poor business practice.
Physical damage from a hammer does not create a repeatable process, does not produce an audit trail, and does not show who handled the device from retirement to destruction. It also introduces safety issues for staff and leaves too much to assumption. Security teams may accept that kind of shortcut at home. Enterprises should not.
Auditors do not reward improvisation.
Should we always choose physical shredding
No. The right method depends on the media type, data sensitivity, device condition, reuse goals, and your internal policy.
Shredding makes sense for failed drives, obsolete media, and assets with no defensible reuse path. Wiping or other approved sanitization methods make more sense when the company wants remarketing value, donation potential, or internal redeployment. That trade-off matters because shredding ends value recovery immediately, while certified sanitization can reduce cost and support circular-economy reporting if the process is documented properly.
The strongest policy is not the most destructive one. It is the one your team can defend under audit and explain to the business without hesitation.
What should be on a Certificate of Destruction
At minimum, it should show the date, method, service location, vendor identity, and a clear tie to the assets destroyed or sanitized. For enterprise use, it should also reference serial numbers or other unique identifiers, the applicable process standard, and enough detail to reconcile the certificate to your internal asset list.
If a certificate reads like a generic receipt, treat that as a warning sign. Weak documentation usually points to weak process discipline behind it.
Can secure data destruction support marketing and CSR goals without sounding opportunistic
Yes, if communications follow verified operational work.
Start with secure handling and credible records. Then report what happened to the assets, what was reused, what was recycled, and what measurable community or environmental outcome came from the project. That sequence keeps the message grounded. It also gives the CIO, sustainability lead, and communications team a shared set of facts.
A vendor relationship can provide significantly more value than a one-time pickup. If your partner can document downstream recycling, support veteran-focused programs, and tie recycling activity to reforestation or similar initiatives, the same project that satisfied security requirements can also support ESG reporting, recruiting, and local brand trust. For Atlanta companies, that is more than a feel-good add-on. It is a way to turn e-waste from a disposal line item into a credible story about stewardship.
If your organization needs a secure, documented, and operationally clean path for retiring IT assets, Atlanta Green Recycling is one Atlanta option for coordinating electronics pickup, secure data destruction, de-installation, and recycling workflows. For companies that also want a stronger ESG and community-impact outcome, ask vendors how they document environmental results and whether they support cause-based programs tied to veteran aid and reforestation.