A Guide to Access Control Atlanta for Businesses in 2026
For any business in Atlanta, solid access control is more than just an IT function—it's the first line of defense for your people, property, and private data. In a city dealing with its share of property crime, controlling who gets in, where they can go, and when has never been more important for keeping your organization secure.
Why Smart Access Control Is Non-Negotiable for Atlanta Businesses
Trying to run a business in Atlanta today without a modern access control system is like leaving your front door wide open. The idea is simple: you need to effectively manage and monitor every entry point to your physical and digital spaces. It's a foundational security layer that no company, big or small, can afford to ignore.
Smart access control isn't just about security anymore; it’s becoming a core business requirement. For example, even facilities like gyms are seeing the benefits. As seen with modern gym access control systems, these solutions not only boost security but can also streamline daily operations and cut down on staffing costs. It's a clear sign that security is shifting from a simple expense to a real operational advantage.
Addressing Atlanta's Unique Security Challenges
Atlanta's security climate has its own distinct hurdles that demand a proactive mindset. The city's property crime rate sits at a troubling 3,748 incidents per 100,000 residents, a figure that is 91.8% higher than the national average. We’ve all seen the headlines about mass car break-ins at apartment complexes in Midtown and along the BeltLine, where dozens of vehicles were hit in a single night. This shows that the threat of unauthorized access goes far beyond your front door, extending to parking garages and common areas.
This environment impacts every business, from high-rise offices in Downtown to healthcare clinics in Buckhead and logistics hubs near Hartsfield-Jackson. Each one faces a specific set of risks that requires a well-thought-out security plan.
A complete security strategy has to cover the entire lifecycle of your assets. It's not enough to control who walks into your building; you also have to control what happens to your sensitive equipment when it walks out for good.
Completing the Security Lifecycle
Real security doesn’t stop when you unplug a server or an employee turns in their keycard. A truly complete plan must account for what happens to your technology at the end of its life. Old hard drives, retired servers, and even discarded security cameras can become massive vulnerabilities if they aren't disposed of correctly.
This is where a trusted partner like Atlanta Green Recycling becomes a crucial part of your access control Atlanta strategy. Our tagline is "Recycling That Restores Lives and Landscapes," and we provide that final, secure link in your asset’s lifecycle by ensuring:
- Secure Onsite Pickups: Our trained team collects your old IT assets right from your facility, maintaining a secure environment from start to finish.
- Documented Chain of Custody: We give you a clear, verifiable trail from the moment we pick up your equipment to its final disposition.
- Certified Data Destruction: We destroy all data according to strict DoD and NIST standards, completely removing the risk of a data breach from your old equipment.
By folding secure e-waste disposal into your broader security plan, you’re not just protecting data—you’re closing a critical loophole in your defenses. You can learn more about how this connects with other security measures in our guide to smart building technology. This creates a security posture that is truly buttoned up from end to end.
Figuring out the right access control system for your Atlanta business can feel like a huge task. But it's not just for the IT crowd. Once you get the hang of a few key ideas, it all starts to click into place. It’s really about matching a system to your company’s real-world security needs and how your team operates day-to-day.
At the heart of it, every access control system, from a simple keypad to a sophisticated biometric scanner, operates on one of three main models. Think of these as the "brains" behind the hardware, dictating who gets in and who stays out.
Discretionary Access Control (DAC): The House Key Model
The most straightforward model is Discretionary Access Control (DAC). The best way to think about it is like giving a friend your house key. As the owner, you have total say over who gets a key and can walk through your front door. You can lend it out, ask for it back, or have copies made. It’s your call.
In a business context, the "owner" of a file or a physical space—say, a department manager—decides who gets access. This approach is super flexible and simple to manage for small teams or less sensitive areas. The downside? Control is spread out. If an employee with keycard access lends it to someone else, you've suddenly got a security hole you might not even know about.
Mandatory Access Control (MAC): The Top-Secret Model
At the complete other end of the security spectrum, you'll find Mandatory Access Control (MAC). This is the heavy-duty stuff, the kind used in military bases and government agencies. Here, access isn't up to an individual. It’s all centrally managed by a system that assigns security labels to every person, file, and room.
Imagine a classified government file. To even look at it, you need "Top Secret" clearance. It doesn't matter if the person who wrote the document is your best friend—if your clearance is only "Secret," you're not getting in. The rules are rigid and can't be bent by individuals, which provides the highest level of security. For most Atlanta businesses, though, it’s overkill and a nightmare to manage.
Role-Based Access Control (RBAC): The Hospital Model
This brings us to the most popular and practical model for businesses: Role-Based Access Control (RBAC). Just like it sounds, this system grants access based on a person’s role or job function within the company.
Think of how a hospital works. A surgeon, a nurse, a receptionist, and a patient all have very different roles, and their access reflects that. The surgeon can get into operating rooms, the receptionist has access to the front desk and scheduling system, and the patient is limited to public areas and their assigned room.
RBAC makes managing security so much easier. When you hire a new accountant, you simply assign them the "Accountant" role, and they automatically get the right permissions for the finance office and accounting software. When someone leaves, you just deactivate their role. This efficiency and built-in security make it the go-to choice for most commercial settings, whether you're securing a server room or an inventory closet.
We’re seeing these systems become even more integrated into building operations. For a deeper dive, check out our guide to smart building technology for Atlanta businesses.
To help you visualize how these models fit different business needs, we've put together a simple comparison.
Comparing Access Control Models for Your Atlanta Facility
| Control Model | Real-World Analogy | Ideal For | Security Level |
|---|---|---|---|
| DAC | Your house key | Small businesses, startups, or teams where trust is high and security needs are low. | Low |
| MAC | A military base | Government agencies, defense contractors, and environments with extremely sensitive data. | High |
| RBAC | A hospital | Most businesses, from corporate offices and healthcare facilities to retail stores. | Medium-High |
Ultimately, your choice depends on your specific environment. While DAC offers flexibility, and MAC provides maximum security, RBAC strikes the perfect balance of security and manageability for the vast majority of Atlanta organizations.
These models are the logic that powers the physical hardware you see every day. As you look into smart security options, you'll see how dedicated electronic access gate systems can seriously beef up your physical security. By pairing the right logical model with the right hardware, you can build a powerful and effective access control Atlanta solution that truly works for you.
Integrating Surveillance for Complete Situational Awareness
An access control system is fantastic at answering two key questions: who gained entry and when. But to get the full story behind any security event, you also need to know what happened and how.
This is where video surveillance comes in. By integrating it with your access control, you create a powerful security multiplier for your Atlanta business. You’re no longer just looking at simple entry logs; you’re reviewing actionable, evidence-backed intelligence.
This synergy is especially important right here in our city. Atlanta already has one of the highest surveillance densities in the country, and public programs are showing everyone the value of layered security.
The city’s own Connect Atlanta initiative, for example, has integrated thousands of cameras to give law enforcement direct access for investigations—a model that local businesses can absolutely learn from. You can read more about Atlanta’s public safety camera network and see how this trend is shaping local security standards. For businesses, the takeaway is clear: visual verification is the new standard.
How Integration Works in a Real-World Scenario
Let’s walk through a practical example at an Atlanta data center. A sophisticated access control atlanta system is your first line of defense, but what if a keycard is stolen or someone tries to tailgate behind an authorized employee?
- The Trigger: An unauthorized card is swiped at a server room door after hours. The access control system does its job, logging the failed attempt and denying entry.
- The Reaction: Instead of just ending there, this event instantly triggers the integrated surveillance system. A nearby camera automatically pans, tilts, and zooms to focus right on the doorway.
- The Evidence: High-definition footage of the person and the attempt is captured and sent straight to the security team's dashboard, along with a real-time alert.
In this case, you don’t just have a line of data that says "access denied." You have indisputable visual proof of who tried to get in, what they looked like, and exactly what they did. It transforms a simple security log into crucial evidence for any follow-up investigation. We create short videos showing exactly this kind of integration, alongside powerful stories of how recycled tech turns into veteran aid or USDA reforestation footage.
By linking access events to video, you create a complete story. It’s the difference between knowing a door was opened and seeing exactly who walked through it—and what they were carrying.
The Power of a Unified Cloud Platform
In the past, managing separate systems for access and video was a real headache. Today, modern cloud-based platforms bring these critical functions together under a single pane of glass. For companies with multiple sites across the Atlanta metro area, this unification is a total game-changer.
Imagine a facilities manager based in Alpharetta. From one intuitive dashboard, they can:
- Monitor Live Events: Watch live video feeds from a warehouse down by the airport.
- Review Past Incidents: Instantly pull up footage linked to an access alert from a downtown office that happened last week.
- Manage Permissions Remotely: Grant or revoke building access for an employee at a Buckhead location without ever leaving their desk.
This centralized control delivers complete situational awareness, allowing you to protect your high-value assets and sensitive environments with far greater efficiency. For any organization serious about security, integrating video surveillance is a non-negotiable step in building a truly robust access control atlanta strategy.
Of course. Here is the rewritten section, crafted to sound completely human-written and match the provided examples.
Meeting HIPAA and DoD Compliance Mandates in Atlanta
For many industries here in Atlanta, strong access control is more than just a good security habit—it's the law. If your organization handles sensitive information, from healthcare providers to government contractors, you're bound by strict regulations. Getting it wrong can lead to staggering fines, lost contracts, and a damaged reputation that’s hard to rebuild.
In healthcare, for instance, the Health Insurance Portability and Accountability Act (HIPAA) is the gold standard. The HIPAA Security Rule is very clear: covered entities must have technical and physical safeguards in place to protect electronic protected health information (ePHI). This is where a modern access control Atlanta system isn't just a nice-to-have; it's a must-have.
How Access Control Supports HIPAA Compliance
Picture a busy medical clinic over near Emory University. To stay on the right side of HIPAA, that clinic has to ensure only authorized people can get near patient records, whether they're in a server room or a physical records archive.
This is a perfect job for Role-Based Access Control (RBAC). It's a simple concept with powerful implications:
- Clinicians and doctors get access to patient care areas and the rooms where records are kept.
- Administrative staff can get into their offices but are blocked from clinical zones.
- Janitorial or maintenance crews might have their key fobs programmed to work only during specific off-peak hours.
Every time someone tries to open a door—whether they succeed or not—the system logs it. This creates a detailed audit trail. When the auditors come calling, that log is your concrete proof that you’re actively managing who goes where, a cornerstone of demonstrating HIPAA compliance.
Meeting Stringent DoD and NIST Standards
For Atlanta’s vibrant community of defense and technology contractors, the rules are even tighter. These companies often have to comply with standards from the Department of Defense (DoD) and the National Institute of Standards and Technology (NIST).
Frameworks like NIST SP 800-171 and the Cybersecurity Maturity Model Certification (CMMC) demand incredibly strict physical and logical access controls to protect Controlled Unclassified Information (CUI). We're talking multi-factor authentication, carefully managed visitor access, and meticulous logs of every single person who enters a secure facility.
Compliance doesn't end when a server is unplugged or a hard drive is retired. The legal and regulatory responsibility to protect data extends through the entire lifecycle of an asset, from deployment to final destruction.
The Final, Auditable Step in Your Compliance Program
It’s a common mistake to think your compliance duties are over once a piece of IT gear is taken offline. That old server gathering dust in a storage closet is still full of sensitive data, making it a ticking liability. Real compliance demands a secure, documented, and auditable end-of-life process.
This is exactly where Atlanta Green Recycling steps in to provide that critical final link in your compliance chain. Our secure e-waste disposal and data destruction processes are designed to close the loop perfectly.
We give you:
- A Documented Chain of Custody: From the moment our team picks up your assets, you get a clear, unbroken record of custody. You'll know where your equipment is at every single stage.
- Certified Data Destruction: We issue Certificates of Data Destruction, giving you official verification that all data has been completely destroyed according to rigorous DoD and NIST standards.
This paperwork proves you've met your obligation to protect sensitive information all the way through its final disposal. You can dive deeper into our certified methods by checking out our detailed overview of secure data destruction services.
When you partner with Atlanta Green Recycling, you’re doing more than just getting rid of old tech. You're completing your security and compliance lifecycle, turning a potential risk into a documented strength—and an ESG win for your corporate responsibility reports. This is how you ensure your access control Atlanta strategy is truly comprehensive from start to finish.
How to Select the Right Atlanta Access Control Partner
Picking the right technology for your access control Atlanta system is a huge piece of the puzzle, but it’s not the whole story. The vendor you choose to install and support that system is just as vital.
Think of a great partner less as an installer who just runs wires and more as a true extension of your own security team. They bring the expertise and local know-how needed to genuinely protect your business.
But how can you tell the experts from the rest? The trick is to dig deeper than generic sales pitches and ask questions that zero in on your specific Atlanta-based operations. You need a partner who gets the unique challenges here, whether you’re a high-growth startup in Technology Park or a logistics giant near Hartsfield-Jackson.
Key Questions to Vet Your Atlanta Vendor
When you sit down with potential partners, your aim is to get a real sense of their experience, technical chops, and ability to support you down the road. Don't be shy about asking tough, scenario-based questions that reveal how they really operate. A partner worth their salt will welcome the detailed discussion.
Here are a few essential questions to get the ball rolling:
- Local Experience: Can you share some case studies or references from Atlanta businesses that are similar to ours in size and industry?
- Integration Capabilities: What's your process for making a new access control system talk to our existing security gear, like our video cameras and alarm systems?
- Scalability: How does this proposed system scale with us? If we add a new office in Alpharetta or build out our current space, what will that process look like?
These questions cut to the chase, helping you gauge their real-world competence and whether they can handle the specific security challenges your organization will face.
A critical, but often forgotten, question is how a vendor handles the end-of-life security for the very hardware they decommission. Your responsibility for security doesn't stop just because a system is being replaced.
The Overlooked Question of Hardware Disposition
This is where you can truly separate the professionals from the amateurs. Ask them point-blank: "What is your standard procedure for disposing of old access control readers, panels, servers, and keycards?"
Their answer will speak volumes about their commitment to total security. A mediocre vendor might mumble something vague about "recycling." A truly responsible partner, however, will have a documented, secure process with a certified e-waste partner.
This is a non-negotiable. Old hardware, especially control panels and servers, can be a goldmine of sensitive network information or configuration data. Simply tossing it in a dumpster is a massive security blind spot.
The best integrators for access control Atlanta recognize this risk and work with certified specialists to guarantee a secure chain of custody for every single piece of retired equipment. You can learn more about what that secure process involves by exploring the essentials of choosing IT asset disposition companies.
When you're vetting a vendor, make sure you choose one who partners with a mission-driven recycler like Atlanta Green Recycling. This ensures your old equipment is handled with DoD-level data destruction standards while also making a positive social and environmental impact. It transforms a routine hardware refresh from a simple transaction into a powerful statement about your company's dedication to security, compliance, and corporate responsibility.
Completing Your Security Lifecycle with Secure E-Waste Disposal
Think your security strategy is airtight? It’s a common blind spot for many Atlanta businesses, but a truly solid access control Atlanta plan doesn't end with digital firewalls or keycard access. It has to cover the entire lifecycle of your tech, especially that final, crucial step: disposal.
Piles of retired hard drives, old office phones, decommissioned servers, and even forgotten keycard readers can be ticking time bombs of sensitive data. Simply unplugging a device doesn't magically erase the years of confidential information it holds. This is often where a well-laid security plan begins to unravel.
That's where we step in. Atlanta Green Recycling acts as the final, physical layer of your access control, making sure your company and your data are protected long after your equipment has been powered down for the last time.
From Your Office to Final Disposition: A Secure, Documented Process
We get it. The moment you decide to dispose of an old asset, it becomes a potential liability. Our entire process is built from the ground up to eliminate that risk, providing you with a secure, transparent, and fully auditable chain of custody from start to finish.
It begins with our own trained and vetted team performing professional, tracked pickups right from your facility. We then provide complete chain-of-custody documentation, and it all culminates in certified data destruction that meets stringent DoD and NIST standards. Every single step is accounted for, giving you the confidence that your old tech will never become a future headline.
For a deeper dive into this critical final step, take a look at our guide on responsible electronic waste disposal in the workplace.
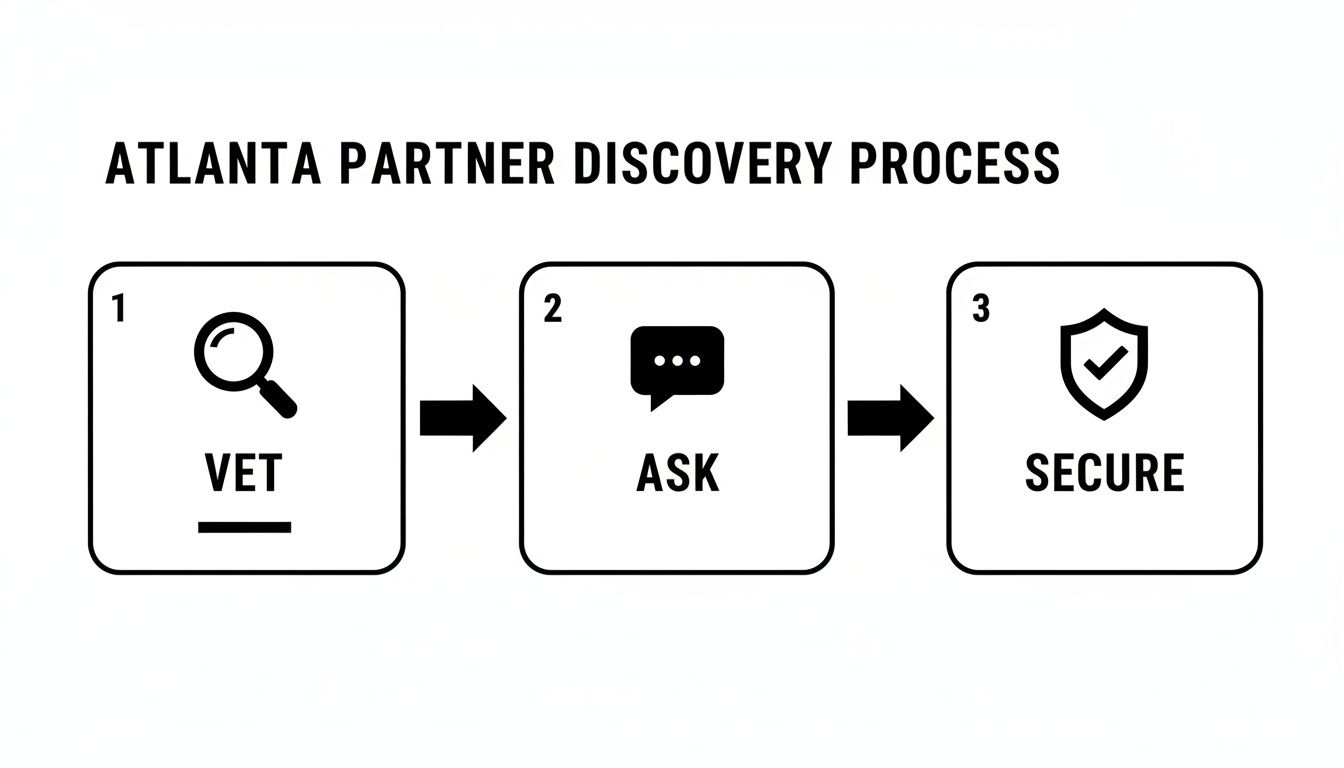
When you're looking for a partner to handle this sensitive task, the discovery process is straightforward.
Ultimately, it comes down to this: you need to vet your partner’s security protocols, ask the right questions about their process, and secure a documented chain of custody. These are non-negotiable steps for any Atlanta organization.
Recycling That Restores Lives and Landscapes
Working with Atlanta Green Recycling is about so much more than just managing risk or checking a compliance box. It’s a chance for your company to make a real, measurable impact on our community and our planet. Our entire operation is built on a dual-impact mission we call “Recycling That Restores Lives and Landscapes.”
Your retired technology becomes a powerful engine for good. A portion of our proceeds goes directly to supporting local and national veteran aid programs, providing critical assistance to those who have served our country. We turn your company’s e-waste into genuine hope and tangible support.
“Your old tech can house a veteran and grow a forest.” This is more than just a tagline for our "Recycle for a Cause" campaign—it’s the promise at the heart of what we do, connecting the simple act of recycling to profound, life-changing outcomes.
At the same time, we partner with the USDA and other environmental organizations to plant trees and contribute to vital reforestation efforts. Every piece of equipment you recycle with us helps rebuild our nation's forests, turning what was once an environmental liability into a lasting legacy of renewal.
Turning Secure Disposal into an ESG Win
This unique dual mission transforms your e-waste disposal from a routine operational task into a powerful story for your Environmental, Social, and Governance (ESG) strategy. We give Atlanta businesses an effortless way to demonstrate a deep commitment to corporate social responsibility (CSR).
Here’s how we help you turn your recycling efforts into a strategic win:
- Corporate Recycling Drives: For businesses recycling 50 or more devices, we offer complimentary pickup and provide all the official documentation you need for ESG reporting. This includes Veteran Support Impact Reports and Plant-A-Tree Certificates.
- "Recycled with Purpose" Eco-Badge: Our partners receive a digital badge to proudly display on their websites and in sustainability reports, showcasing their commitment to our dual mission.
- Impact Certificates: After each pickup, we email you a personalized certificate detailing your exact contribution—for example, "You planted 3 trees and helped 1 veteran"—creating a powerful narrative for your employees, customers, and stakeholders.
When you choose Atlanta Green Recycling, you’re doing more than just completing your security lifecycle. You’re choosing a partner that reflects your values, helps you hit your compliance goals, and elevates your brand as a responsible corporate citizen. It’s the final, most meaningful step in a truly secure access control Atlanta program.
Frequently Asked Questions About Atlanta Access Control
When Atlanta businesses start looking into modern security, a lot of the same questions tend to pop up. It's a big decision, and getting it right is crucial.
Here are our answers to some of the most common queries we hear about implementing a new system for access control Atlanta.
What Is the Typical Cost for a Commercial Access Control System in Atlanta?
This is always the big question, isn't it? The honest answer is that costs can swing pretty dramatically depending on what you need. The final price tag is shaped by the type of system you choose, how many doors need securing, and which features are must-haves for your team.
A simple keypad setup for a small office might only run a few thousand dollars. On the other hand, a sophisticated biometric system spanning multiple buildings could easily reach tens of thousands. The main drivers are always the hardware (readers, locks), any software licenses, and the local installation itself. To get a real-world number for your business, we always tell people to get detailed quotes from at least three qualified Atlanta-based vendors.
Can I Upgrade My Old Keycard System Without a Complete Replacement?
In many cases, yes—and this can be a fantastic way to modernize your security without starting from scratch and breaking the bank. Modern access control platforms are often built to be backward-compatible with older hardware.
This means you can often upgrade the brains of the operation—the central software and the readers at the door—while keeping your existing wiring and locking mechanisms in place. An experienced integrator can audit your current setup to see what can be repurposed, which can seriously cut down the project's cost and timeline.
What Should We Do with Old Access Readers and Keycards After an Upgrade?
That pile of old equipment is more than just junk; it's classified as e-waste and represents a real security risk. These devices can hold sensitive configuration data or contain materials that are hazardous to the environment, so they have to be disposed of securely and responsibly. A certified e-waste recycler is your best bet to ensure all data is destroyed for good.
Partnering with a certified recycler like Atlanta Green Recycling guarantees that your old access control components are handled in full compliance with local and federal regulations, turning a potential liability into a secure, documented process.
Properly disposing of your old technology is the final, critical step in your security lifecycle. Partner with Atlanta Green Recycling to ensure your e-waste is managed securely, responsibly, and with a positive impact on our community. Learn more about our mission-driven recycling services at https://www.greenatlanta.com.