A Guide to Secure HDD Disposal for Atlanta Businesses
Hitting 'delete' on old hard drives and calling it a day is a recipe for disaster. To truly protect your company's sensitive information, you need certified data destruction—a process that permanently and verifiably eliminates every last bit of data. This isn't just about cleaning up old equipment; it's about making sure your retired hard drives don't become the source of your next costly data breach. Our mission is simple: Recycling That Restores Lives and Landscapes.
Why Secure HDD Disposal Is a Business Imperative
When a computer, server, or storage device has run its course, what actually happens to the hard drive inside? It's a question many Atlanta businesses overlook, but that oversight can create massive risk. Think about it: every single hard drive is a vault of sensitive history. It holds financial records, private employee information, intellectual property, and confidential client details.
For a cybercriminal, an improperly discarded drive is a goldmine. The fallout from a breach can be brutal, from the financial sting of regulatory fines under laws like HIPAA or FACTA to the long-term damage to your company's reputation. If you’re serious about protecting your assets, your Data Loss Prevention strategies absolutely must extend to the physical end-of-life of your storage media. This isn't just an IT task anymore—it's a non-negotiable part of modern corporate governance.
The Growing Need for Certified Destruction
We're seeing a major shift in how businesses approach data security, and the numbers back it up. The global market for professional hard drive destruction services was valued at USD 1.5 billion in 2023 and is on track to hit USD 3.6 billion by 2032.
This isn't just a trend; it's a clear signal that secure, certified disposal has moved from a "nice-to-have" to a core business function. Working with a certified partner like Atlanta Green Recycling gives you peace of mind and, just as importantly, an auditable trail that proves you’ve done your due diligence.
Turning Compliance into a Powerful Brand Statement
Of course, the primary goal here is to mitigate risk. But what if you could turn a compliance necessity into something that strengthens your brand and serves the community? At Atlanta Green Recycling, we believe you can. We’ve built our entire model around connecting secure electronics disposal with real-world social and environmental impact.
Our “Recycle for a Cause” mission is simple but powerful: “Your old tech can house a veteran and grow a forest.” We transform a standard operational task into a meaningful contribution to your company's Environmental, Social, and Governance (ESG) goals.
When you partner with us, you're not just securely destroying data—you're making a tangible difference. That commitment resonates with customers, engages employees, and gives you a compelling story for your corporate social responsibility reports. You’re not only locking down your data but also embracing the full benefits of e-waste recycling by supporting causes that truly matter. We turn e-waste into hope.
Decoding Data Destruction Methods and Standards
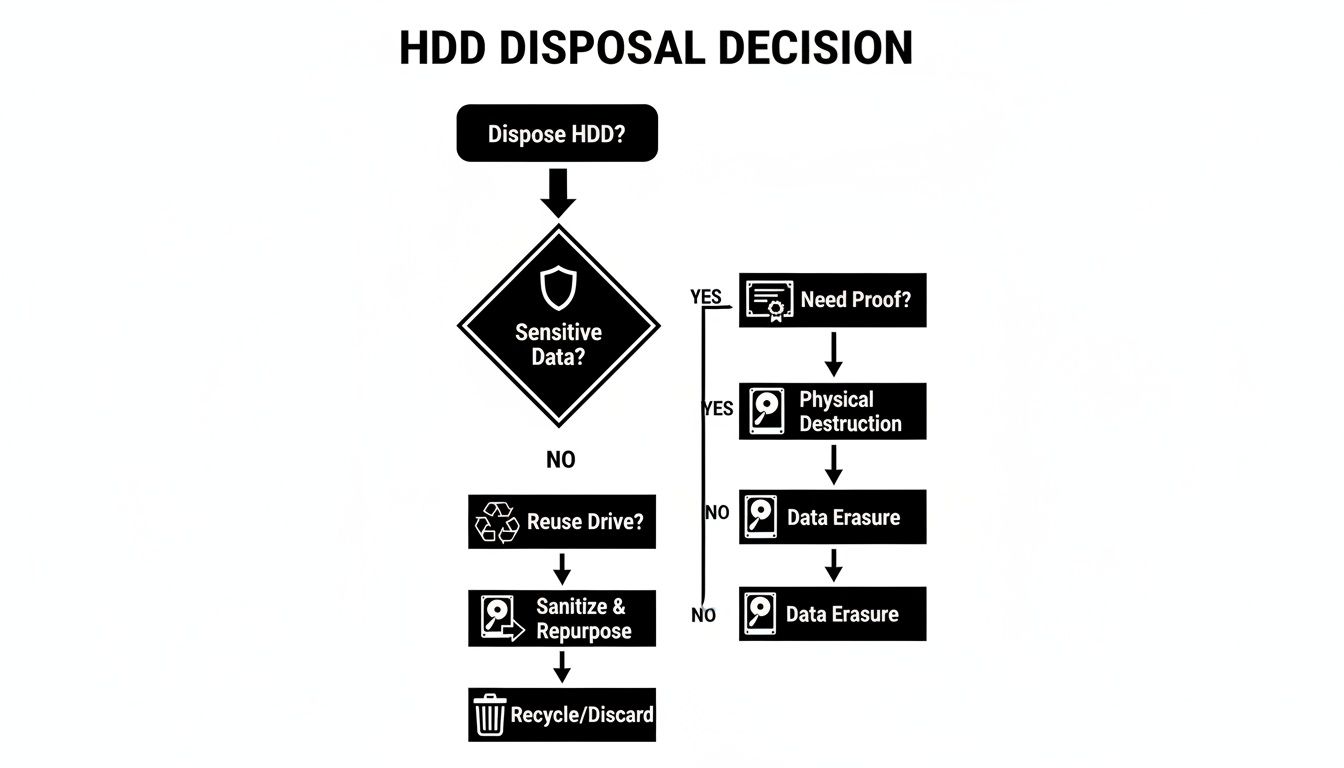
Once a hard drive is flagged for disposal, the real work begins. How do you guarantee the data on it is truly gone for good? Just hitting "delete" or reformatting a drive is a rookie mistake that leaves data wide open for recovery. Proper, secure HDD disposal relies on methods that make that information permanently and verifiably inaccessible.
Getting a handle on these methods helps your organization pick the right play based on data sensitivity, what you plan to do with the hardware next, and your specific compliance checklist. Let's break down the three core techniques we use in the field.
Software Wiping for Secure Reuse
Software wiping, often called overwriting or data erasure, uses specialized software to systematically write patterns of ones and zeros over every single sector of a hard drive. It’s like painting over a canvas so completely that the original image is impossible to see.
This is the go-to method when you want to reuse, redeploy, or resell the hard drives. Because the drive stays physically intact and fully functional, it keeps its asset value. For a deeper dive into the specific standards and processes, you can learn more about the complete process of data sanitization in our detailed guide.
Degaussing for Magnetic Media
Degaussing is a brute-force approach specifically for magnetic storage like traditional HDDs and old-school magnetic tapes. A degausser unleashes a powerful magnetic field that instantly scrambles the magnetic charge on the drive's platters, wiping the data clean in a flash.
It's incredibly fast and effective, but there's a catch: it renders the hard drive totally useless afterward. Degaussing is a solid choice when the drive's life is over and you need an extremely high level of security before it heads to the shredder. It's crucial to know, however, that this method has zero effect on Solid-State Drives (SSDs), which don’t use magnetic storage.
Physical Shredding: The Ultimate Failsafe
When there is absolutely no room for error, nothing beats physical destruction. This is exactly what it sounds like: we feed hard drives into a massive industrial shredder that grinds them into small, mangled pieces of metal and plastic.
Once a drive is shredded, pulling any data from that pile of fragments is a physical impossibility.
Key Takeaway: Physical shredding is the gold standard for secure HDD disposal. It offers irreversible destruction and is the required method for devices holding top-secret intellectual property, classified government data, or protected health information (PHI).
Shredding provides undeniable, visual proof that the media has been destroyed. That finality is exactly what strict regulatory frameworks demand.
As you can see, the right path forward depends on whether the drive has a future, how sensitive the data is, and what level of proof your compliance officer needs to see.
Comparing Data Destruction Methods
To make the choice clearer, here’s a quick rundown of how these three methods stack up against each other. Each has its place, and the best fit depends entirely on your end goal—be it asset recovery, absolute security, or a bit of both.
| Method | Description | Best For | Compliance Level | Reuse Potential |
|---|---|---|---|---|
| Software Wiping | Overwrites all data on the drive with random characters, making original data unrecoverable. | Reusing or reselling HDDs; managing IT assets with remaining value. | High (Meets NIST 800-88 Purge standard) | Yes |
| Degaussing | Uses a powerful magnetic field to erase data on magnetic media like HDDs and tapes. | Quickly sanitizing large batches of magnetic drives before physical destruction. | Very High (Meets NIST 800-88 Purge for magnetic media) | No |
| Physical Shredding | Grinds the hard drive into small metal fragments, making data retrieval physically impossible. | End-of-life drives with highly sensitive data; meeting the strictest compliance rules. | Absolute (Meets NIST 800-88 Destroy standard) | No |
Ultimately, this table shows there's no single "best" method, only the right method for your specific situation.
Understanding Key Compliance Standards
Your choice of destruction method isn't just a technical decision—it's a compliance one. Auditors don't just ask if you destroyed data; they want to know how, and if it lines up with established industry frameworks.
In the U.S., the benchmark is NIST Special Publication 800-88, "Guidelines for Media Sanitization." This isn't just some obscure government paper; it's the foundational document that sets the standard for a risk-based approach to data destruction.
NIST 800-88 outlines three distinct levels of sanitization:
- Clear: Uses basic read/write commands to overwrite data. Good enough for protection against simple recovery attempts.
- Purge: A more robust process using techniques like cryptographic erase or patterned overwriting to thwart advanced, laboratory-level recovery attacks.
- Destroy: The final option. This involves physically disintegrating, pulverizing, melting, or shredding the media until data recovery is impossible.
Aligning your disposal process with NIST guidelines is the best way to ensure it will hold up under the microscope of an audit. Working with a certified vendor who not only understands these standards but also documents every step accordingly is the key to proving your due diligence.
Choosing Your Disposal Strategy: On-Site vs. Off-Site
Once you’ve figured out how you're going to destroy your data, the next big question is where it’s all going to happen. The choice between on-site and off-site secure HDD disposal really comes down to balancing your company's unique needs for security, convenience, budget, and logistics. Each route has its clear advantages, and the right one depends entirely on your specific situation.
Making this call means taking a hard look at your internal policies and the regulations you're up against. There's no single right answer here, but understanding the trade-offs will point you to the strategy that best protects both your data and your bottom line.
The Case for On-Site Destruction
On-site destruction is exactly what it sounds like—the whole process comes directly to you, usually in the form of a mobile shredding truck. This approach gives you the ultimate level of transparency and control. Your team can literally stand there and watch every single hard drive get turned into fragments before it ever leaves your property.
For organizations in highly regulated fields, that kind of direct oversight is often non-negotiable.
- Maximum Security and Control: The chain of custody is about as short as you can get. It goes from your data center straight to the shredder parked out back. This just about eliminates any risks that come with transporting live, data-bearing assets.
- Immediate Verification: You get a Certificate of Destruction right then and there, confirming that your media has been successfully and completely sanitized.
- Compliance Peace of Mind: For sectors governed by tough regulations like HIPAA or FACTA, or even just strict internal security rules, witnessing the destruction firsthand provides undeniable proof of due diligence for any auditor.
We once worked with an Atlanta-based law firm that needed to dispose of 200 hard drives packed with sensitive client case files. For them, having their IT director and a partner watch the entire process from start to finish was the deciding factor. It ensured they met their ethical and legal duties with zero ambiguity.
If your organization puts absolute, verifiable security above everything else, then looking into professional on-site shredding services is a smart next step.
The Advantages of Off-Site Services
While on-site services deliver unmatched transparency, off-site destruction brings its own benefits to the table, namely in convenience, scalability, and often, cost. In this model, a certified vendor manages all the secure logistics—packing, collecting, and transporting your assets to their specialized facility for destruction. We even offer businesses free pickup for 50+ devices.
This is the go-to approach for massive projects where trying to manage the process in-house would be a logistical nightmare. Just imagine a data center decommissioning involving thousands of drives. An off-site partner can handle that entire workflow efficiently, from de-installation all the way to the final report.
The hard disk destruction equipment market shows a clear demand for these professional solutions. The commercial use segment alone is valued at roughly USD 450 million. Businesses invest heavily in certified vendors because they have to meet mandatory compliance rules and face huge liability if a breach happens, making both on-site and off-site services critical. You can get more insight into the hard disk destruction market drivers and trends if you're curious.
Making the Right Choice for Your Atlanta Business
So, how do you decide? The best strategy really hinges on how you answer a few key questions.
- What is your risk tolerance? If your data is so sensitive that you can't accept even the slightest risk of it being transported, on-site is the obvious winner.
- What is the scale of your project? For smaller batches or routine clear-outs, on-site is perfectly manageable. But for decommissioning hundreds or even thousands of assets, the logistics of an off-site service are far more practical.
- What does your budget look like? Off-site services can sometimes be more budget-friendly due to the economies of scale at the vendor's facility. On-site services, on the other hand, carry a premium for the convenience and absolute security of mobile operations.
By weighing these factors, you can confidently pick a secure HDD disposal strategy that lines up perfectly with your company's operational needs and compliance mandates.
The Critical Role of Audit-Ready Documentation
Secure HDD disposal doesn't truly end when a hard drive is shredded or degaussed. For your compliance officer or auditor, that's actually where the most important part begins. Without a clear, comprehensive paper trail, all your careful destruction efforts are essentially undocumented, leaving your organization wide open during an audit.
This documentation is your ultimate defense. It’s what transforms a physical act into a legally defensible record, proving you fulfilled your duty of care and protecting your Atlanta business from the steep fines and reputational fallout of a compliance failure. It’s not just about having papers on file; it's about having the right papers, with specific, verifiable details that stand up to scrutiny.
Establishing an Unbroken Chain of Custody
From the moment a hard drive leaves your physical control, its journey must be meticulously logged. This is the entire point of a chain of custody record. Think of it as a chronological diary that documents every single touchpoint—who handled the assets, where they were stored, how they were transported, and when they were finally destroyed.
A truly robust chain of custody form has to include:
- Asset Identification: A detailed manifest of every single device, including its make, model, and—most importantly—its unique serial number.
- Pickup Details: The exact date, time, and address of collection, along with the signature of the employee who released the assets.
- Secure Transport: Confirmation that all assets were moved in locked, sealed containers by authorized personnel.
- Arrival Confirmation: Verification of the date and time the assets arrived at the secure destruction facility, including the signature of the receiving technician.
This document leaves no room for ambiguity. It creates a seamless, accountable record from your office all the way to the point of final disposition.
The Power of the Certificate of Destruction
The final, and arguably most critical, piece of this puzzle is the Certificate of Destruction (CoD). This is not just a receipt. It's a formal, legally significant attestation that your data has been permanently and irreversibly destroyed according to specific industry standards. If your business is serious about verifiable data security, understanding the ISO 27001 audit process can offer some valuable context on why this kind of documentation is absolutely non-negotiable.
A valid CoD is your proof of compliance, but only if it contains the right information.
A proper Certificate of Destruction should be far more than a simple statement. It must function as a detailed affidavit, providing an auditor with every piece of information needed to verify the secure disposal process from beginning to end.
So, what gives a CoD its legal weight? Look for these key elements:
- Unique Certificate Number: A serialized number for easy tracking and verification.
- Client Information: Your company’s official legal name and address.
- Vendor Information: The certified destruction partner’s name, address, and contact details.
- Itemized Asset List: A complete inventory of every piece of media that was destroyed, cross-referenced by serial number to the chain of custody log.
- Destruction Method: A clear statement of the process used (e.g., physical shredding to 2mm particles, degaussing) and the compliance standard it meets (e.g., NIST 800-88 Purge).
- Date and Location: The specific date and physical location where the destruction took place.
- Authorized Signature: The signature of a representative from the destruction vendor, attesting that all information provided is accurate.
You can learn more about what makes a document effective by reviewing our guide on the hard drive certificate of destruction. With these components in place, your CoD becomes a powerful risk management tool, offering the peace of mind that comes from knowing your secure HDD disposal process isn't just complete—it's fully defensible.
Partnering for Secure and Socially Responsible Disposal
Choosing a partner for secure HDD disposal in Atlanta isn't just about ticking compliance boxes. It's a chance to turn a routine operational task into a powerful statement about your company's values. The right partner doesn’t just destroy data; they deliver peace of mind, audit-ready proof, and a compelling story that boosts your brand's reputation and supports your ESG (Environmental, Social, and Governance) goals. We help you target keywords like “electronics recycling for veterans,” “Atlanta tech recycling,” and “corporate sustainability electronics disposal.”
A truly effective partnership offers a turnkey solution that handles every detail, from secure logistics and certified destruction to meticulous reporting. This frees up your team to focus on their core jobs instead of wrestling with complex IT asset disposition. More importantly, it flips the script from a cost center to a value-add, where your end-of-life tech becomes a catalyst for real community impact.
From Compliance Requirement to ESG Cornerstone
Today’s consumers and employees expect more. They want to see a genuine commitment to social and environmental responsibility from the companies they do business with and work for. Your secure HDD disposal process is a perfect—and often overlooked—opportunity to show that commitment in a tangible way.
Imagine being able to tell your stakeholders, “Your old tech can house a veteran and grow a forest.” That isn't just a clever tagline; it's a direct result of a strategic partnership. By choosing a vendor with a dual-impact mission, you turn e-waste into a resource that helps restore both lives and landscapes. We make meeting your ESG and CSR goals easy.
This approach transforms secure disposal into a cornerstone of your corporate social responsibility. It provides a powerful, authentic story for your annual reports, engages employees in a mission they can be proud of, and resonates deeply with a customer base that values purpose-driven brands.
This is a significant shift. The demand for certified, compliant data destruction is already skyrocketing, driven by escalating cybersecurity threats and tough regulations. In fact, the secure data destruction market is projected to hit USD 5.45 billion by 2029, a clear sign that businesses are taking this seriously. You can explore the key drivers of the data destruction market to see the global push for better security. By layering social impact on top of this security imperative, you create a powerful competitive edge.
The Tangible Proof of a Purpose-Driven Partnership
A mission-driven disposal program is only as good as the proof that backs it up. A credible partner must provide clear, transparent documentation not just of data destruction, but also of the social and environmental outcomes your contribution has enabled. This is where the real value lies for your ESG reporting.
Look for a partner that provides a full suite of impact documentation:
- Veteran Support Impact Reports: Detailed summaries that quantify how your recycled assets have contributed to veteran aid programs—perfect for CSR documentation.
- Plant-A-Tree Certificates: Personalized certificates confirming the number of trees planted in your company’s name, giving you a concrete environmental metric to share.
- An Eco-Badge for Your Brand: A digital “Recycled with Purpose” badge you can display on your website and sustainability reports to signal your commitment to stakeholders.
These elements provide the social proof needed to build trust and credibility. For example, a live impact counter on a partner’s website showing stats like “1,245 veterans supported” and “3,700 trees planted” reinforces transparency and shows the collective impact of their community. We can also create short videos showing veterans receiving aid or USDA reforestation footage to tell your company's impact story.
Choosing the Right Atlanta Partner for Your Needs
When evaluating potential partners in the Atlanta area, you have to look beyond the basic service list. You need a vendor who understands the unique intersection of absolute data security and meaningful social responsibility. They should function as an extension of your team, dedicated to protecting your data while amplifying your positive impact. We co-host recycling drives with VFW chapters and partner with schools under a "Greener Atlanta" initiative.
To make an informed decision, consider asking potential vendors these questions:
- How do you document the chain of custody for both security and social impact?
- Can you provide case studies showing how you've helped other Atlanta companies meet their ESG benchmarks through electronics disposal?
- What kind of reporting and certification will we receive to use in our corporate sustainability reports?
- Do you partner with local veteran or environmental nonprofits to maximize community engagement?
The right partnership makes secure HDD disposal effortless and rewarding. It ensures your data is protected by the highest standards while turning your obsolete IT assets into a force for good. If you're looking to simplify your process, our complete guide on how to choose among the top IT asset disposition companies can provide further valuable insights for making the right choice.
Your Hard Drive Disposal Questions, Answered
Even after you've mapped out a disposal strategy, a few specific questions always seem to pop up. We get it. The details matter, especially when compliance and data security are on the line. To clear up any lingering uncertainty, here are some straightforward answers to the questions we hear most often from businesses right here in Atlanta.
Wiping vs. Shredding: What's the Real Difference?
The core difference boils down to one simple question: will the drive be used again?
Wiping, often called software overwriting, is a deep-cleaning process. It systematically writes new, meaningless data over every single sector of the hard drive, making the original information practically impossible to recover with software. This is the perfect path for drives you intend to reuse, sell, or redeploy somewhere else in your organization.
Shredding is the final chapter. It's the physical annihilation of the drive, turning it into a pile of mangled metal and plastic fragments. There's no coming back from this. Shredding makes data recovery a physical impossibility, which is why it's the undisputed champion for any end-of-life media that held sensitive IP, PII, or other regulated data.
Do I Really Need a Certificate of Destruction?
Yes, absolutely. While a Certificate of Destruction (CoD) might not be explicitly named in every regulation, it functions as your official, auditable proof that you upheld your duty of care. When auditors come knocking or, worse, a data breach investigation begins, that CoD is your first and best line of defense. After donation, we also automatically email you personalized impact certificates (“You planted 3 trees and helped 1 veteran”).
Think of a Certificate of Destruction not as a simple receipt, but as a critical piece of your risk management strategy. It's the document that shields you from the crushing fines, legal battles, and reputational fallout that come with a compliance failure.
How Is My Data Kept Safe During Off-Site Transport?
This isn't like calling a standard courier. A reputable data destruction partner operates on a strict, unbroken chain-of-custody protocol. From the moment we arrive at your facility, it's a tightly controlled and documented process.
Here's what that looks like in practice:
- Serialized Asset Tracking: Every single drive, server, or device is scanned and logged by its unique serial number before it ever leaves your building.
- Secure, Locked Transport: Assets are placed in locked, tamper-evident containers for the journey.
- GPS-Monitored Vehicles: Our trucks are tracked in real-time, ensuring we know their location from your door to ours.
- Documented Handoffs: Every time custody changes hands, it's signed for, creating a clear, unbroken, and accountable paper trail.
From the second your drives leave your possession, they are tracked, secured, and accounted for until the moment they are verifiably destroyed.
What Does Secure HDD Disposal Cost in Atlanta?
The price for professional hard drive disposal can shift based on a few key variables—how many drives you have, the method you choose (on-site shredding is priced differently than off-site), and any unique logistical needs. But it's crucial to view this cost as an investment, not an expense.
The operational cost of certified, professional destruction is just a fraction of the catastrophic financial damage a data breach can cause. A single incident can spiral into millions of dollars in regulatory penalties, legal fees, and customer notifications, not to mention the lasting harm to your brand. We provide clear, customized quotes that match your security requirements and budget, so you get the protection you need without any surprises.
Ready to make your IT asset disposal process secure, compliant, and genuinely impactful? At Atlanta Green Recycling, we offer complete solutions that don't just guarantee the highest standard of data security—they also help you achieve your corporate social responsibility goals. Let's work together to protect your data, support our veterans, and help reforest our communities. Schedule your secure electronics pickup today.